Use ASI1 as the default model in OpenClaw
This guide follows the interactive OpenClaw setup wizard (QuickStart) and connects ASI:One as a Custom Provider using the OpenAI-compatible endpoint https://api.asi1.ai/v1 and model asi1. You can also configure the same settings by editing the config file manually.
The screenshots in this page are for UI flow only — any key visible there is for demonstration; use your own key on your machine. If a key was ever exposed (chat, screenshot, repo), rotate it in the ASI:One / asi1.ai dashboard and update OpenClaw config.
What you need
| Item | Notes |
|---|---|
| OpenClaw | Installed via the official installer (see below). |
| ASI:One API key | Create one in the ASI:One quickstart. |
| Network | Access to https://api.asi1.ai from the machine running the gateway. |
Step 1 — Install OpenClaw
Run the official installer (macOS/Linux). It checks Node.js, npm, and Git, then installs the OpenClaw CLI and starts setup.
curl -fsSL https://openclaw.ai/install.sh | bash
When installation finishes, the OpenClaw setup wizard opens in the terminal.
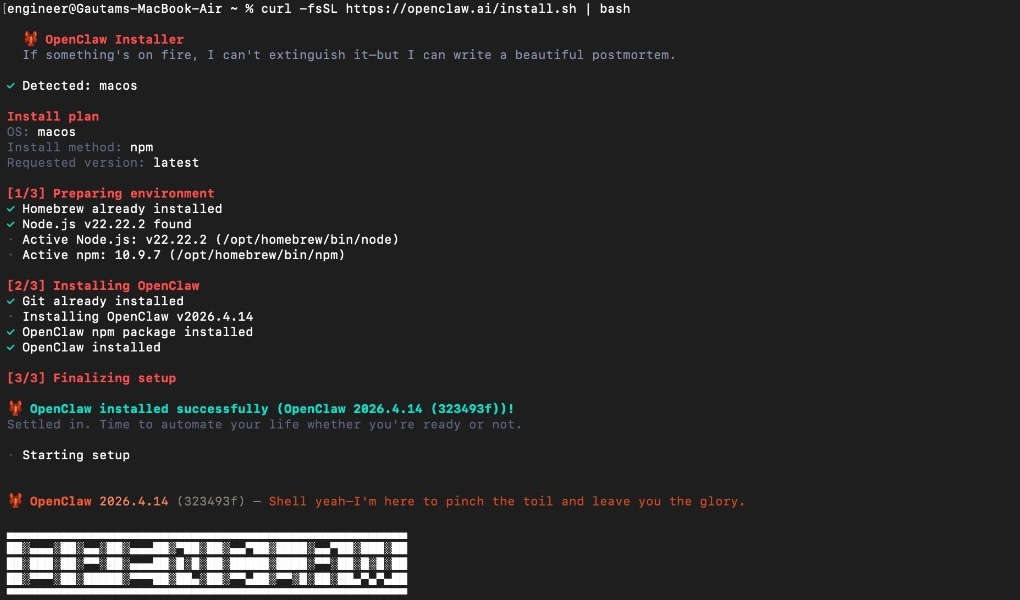
Example: installer summary and OpenClaw banner. Your version string may differ (e.g. OpenClaw 2026.4.14).
Step 2 — Security acknowledgement
Read the Security notice. OpenClaw is a powerful local agent; understand gateway security before exposing tools or chat channels.
Answer Yes to continue after you accept the personal-by-default risk model.
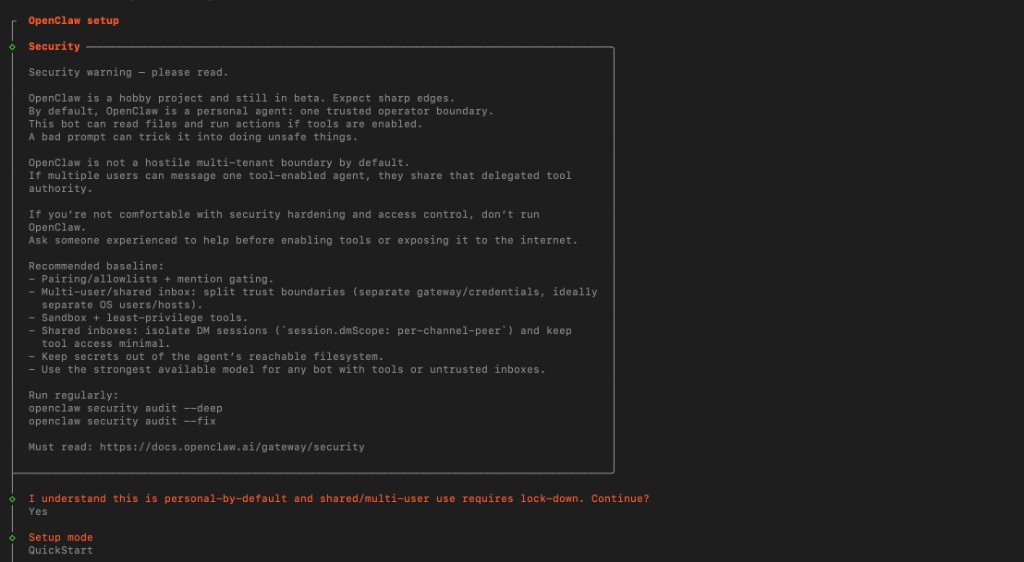
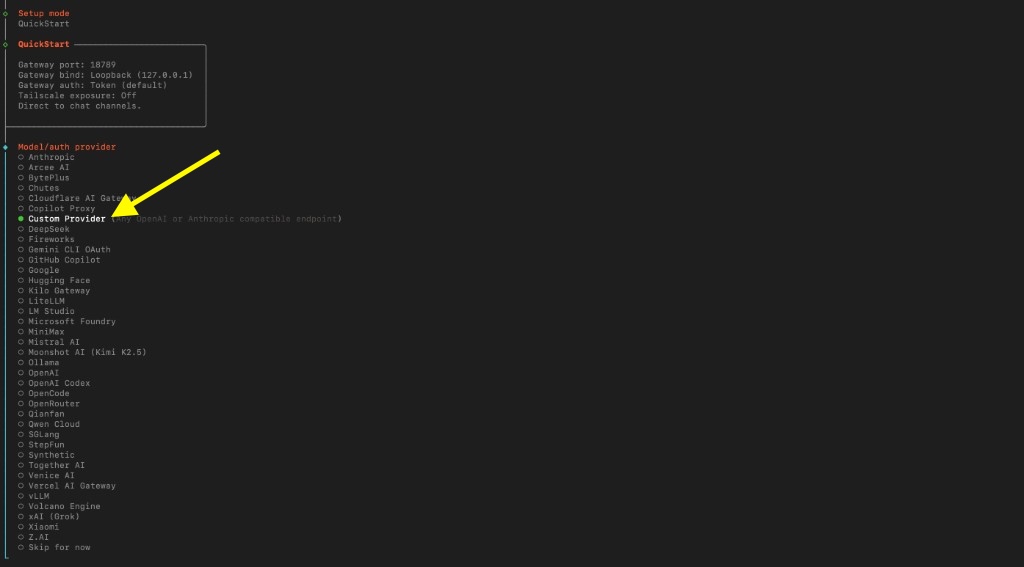
Step 3 — Setup mode: QuickStart
Choose QuickStart. The wizard shows defaults for the local gateway, for example:
| Setting | Typical QuickStart value |
|---|---|
| Gateway port | 18789 (example from wizard) |
| Gateway bind | Loopback (127.0.0.1) |
| Gateway auth | Token (default) |
| Tailscale exposure | Off |
| Flow | Direct to chat channels |
Exact values can change with OpenClaw versions; follow what your wizard displays.
Step 4 — Model / auth provider: Custom Provider
Select Custom Provider (any OpenAI- or Anthropic-compatible endpoint). ASI:One exposes an OpenAI-compatible HTTP API, so this is the right option.
Step 5 — ASI:One endpoint and API key
Enter the following when prompted.
| Wizard prompt | Value for ASI:One |
|---|---|
| API Base URL | https://api.asi1.ai/v1 |
| How do you want to provide this API key? | Paste API key now (stores the key in OpenClaw config) or Use external secret provider (recommended for shared machines) |
| API Key | Paste your ASI:One key (leave blank only if the endpoint truly needs no key). |
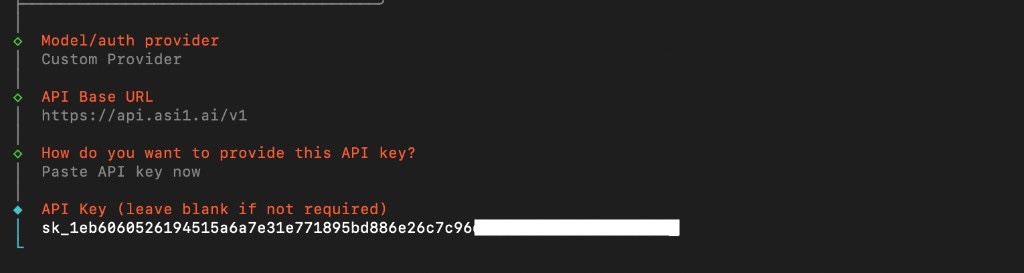
When you paste API key now, OpenClaw stores it locally (see warning at top). Do not commit ~/.openclaw/openclaw.json or share it.
Key storage options (detail)

| Option | When to use |
|---|---|
| Paste API key now | Fastest; key is stored in local OpenClaw config. |
| Use external secret provider | Better when you do not want the key in plaintext config. |
Step 6 — Compatibility and model name
After the key step, the wizard continues with checks similar to:
| Prompt | ASI:One value |
|---|---|
| Endpoint compatibility | OpenAI-compatible |
| Model ID | asi1 |
The wizard verifies the endpoint (Verification successful).
It then assigns an Endpoint ID (an internal name for this custom endpoint). In a real run this looks like a unique slug, for example innovationlab-api-asi1-ai — yours may differ.
| Prompt | Notes |
|---|---|
| Endpoint ID | Wizard-generated id for this provider entry. |
| Model alias (optional) | Friendly label in pickers; skip if unsure. |
At the end you should see a line like:
Configured custom provider: <your-endpoint-id>/asi1
So the full model reference is always <endpoint-id>/asi1. If you named the endpoint asi1 during manual config, that becomes asi1/asi1 — same pattern, different first segment.
Step 7 — Channels (QuickStart)
QuickStart continues with channel status (Discord, Telegram, Slack, etc.). Connecting a channel is optional for testing the model; see OpenClaw channels for pairing, tokens, and security (DM pairing, dmPolicy, etc.).
Concepts (quick reference)
| Term | Meaning |
|---|---|
| Endpoint ID | Name OpenClaw uses for this custom provider in config (wizard-assigned or chosen in advanced flows). |
| Model ref | <endpoint-id>/asi1 — must match registered model id asi1. |
| OpenAI-compatible | Same HTTP shape as OpenAI Chat Completions (/v1, etc.). |
Manual config (equivalent JSON5)
If you prefer files over the wizard, merge something like this into ~/.openclaw/openclaw.json. Replace provider key asi1 with your Endpoint ID if the wizard created a different slug.
{
env: {
ASI1_API_KEY: "YOUR_ASI_ONE_API_KEY",
},
agents: {
defaults: {
model: { primary: "asi1/asi1" },
},
},
models: {
mode: "merge",
providers: {
asi1: {
baseUrl: "https://api.asi1.ai/v1",
apiKey: "${ASI1_API_KEY}",
api: "openai-completions",
models: [
{
id: "asi1",
name: "ASI1",
reasoning: false,
input: ["text"],
contextWindow: 128000,
maxTokens: 8192,
},
],
},
},
},
}
Config keys
| Key | Role |
|---|---|
models.providers.<id> | Provider slug — must match the first segment of agents.defaults.model.primary. |
baseUrl | https://api.asi1.ai/v1 |
api | "openai-completions" |
models[].id | asi1 (ASI:One model name) |
CLI: set default model only
If the provider already exists:
openclaw config set agents.defaults.model.primary <your-endpoint-id>/asi1
Verify
openclaw models list --provider <your-endpoint-id>
You should see model asi1 listed for that provider.
Python (sanity check)
Same endpoint and model as OpenClaw:
from openai import OpenAI
client = OpenAI(
api_key="YOUR_ASI_ONE_API_KEY",
base_url="https://api.asi1.ai/v1",
)
response = client.chat.completions.create(
model="asi1",
messages=[{"role": "user", "content": "Hello!"}],
)
Troubleshooting
| Issue | What to check |
|---|---|
| Verification fails | baseUrl ends with /v1, key is valid, outbound HTTPS to api.asi1.ai. |
| Wrong model ref | Default must be <endpoint-id>/asi1 with models[].id = asi1. |
| Key in repo | Never commit openclaw.json with pasted keys. |
Related
| Page | Topic |
|---|---|
| fetch-agents skill | Agentverse from OpenClaw |
| ASI:One OpenAI Compatibility | Chat API |
| ASI:One API reference | Limits and parameters |
| OpenClaw providers | Upstream provider list |
| OpenClaw model providers | Custom baseUrl |